Chinese govt hackers breached telcos to snoop on network traffic
[ad_1]

Several US federal agencies today revealed that Chinese-backed threat actors have targeted and compromised major telecommunications companies and network service providers to steal credentials and harvest data.
As the NSA, CISA, and the FBI said in a joint cybersecurity advisory published on Tuesday, Chinese hacking groups have exploited publicly known vulnerabilities to breach anything from unpatched small office/home office (SOHO) routers to medium and even large enterprise networks.
Once compromised, the threat actors used the devices as part of their own attack infrastructure as command-and-control servers and proxy systems they could use to breach more networks.
“Upon gaining an initial foothold into a telecommunications organization or network service provider, PRC state-sponsored cyber actors have identified critical users and infrastructure including systems critical to maintaining the security of authentication, authorization, and accounting,” the advisory explains.
The attackers then stole credentials to access underlying SQL databases and used SQL commands to dump user and admin credentials from critical Remote Authentication Dial-In User Service (RADIUS) servers.
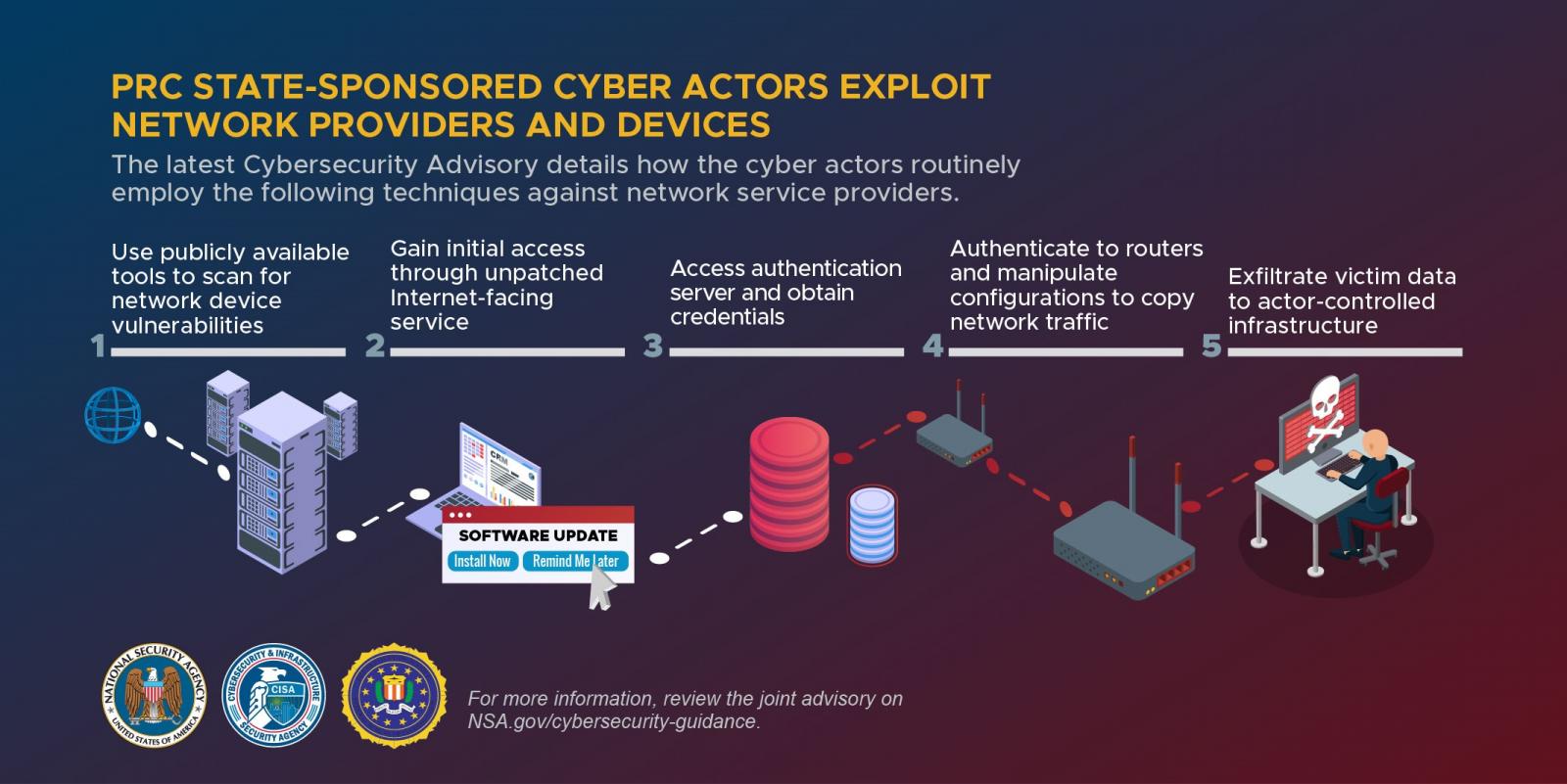
“Armed with valid accounts and credentials from the compromised RADIUS server and the router configurations, the cyber actors returned to the network and used their access and knowledge to successfully authenticate and execute router commands to surreptitiously route, capture, and exfiltrate traffic out of the network to actor-controlled infrastructure,” the federal agencies added.
The three federal agencies said the following common vulnerabilities and exposures (CVEs) are the network device CVEs most frequently exploited by Chinese-backed state hackers since 2020.
“The PRC has been exploiting specific techniques and common vulnerabilities since 2020 to use to their advantage in cyber campaigns,” the NSA added.
| Vendor | CVE | Vulnerability Type |
| Cisco | CVE-2018-0171 | Remote Code Execution |
| CVE-2019-15271 | Remote Code Execution | |
| CVE-2019-1652 | Remote Code Execution | |
| Citrix | CVE-2019-19781 | Remote Code Execution |
| DrayTek | CVE-2020-8515 | Remote Code Execution |
| D-Link | CVE-2019-16920 | Remote Code Execution |
| Fortinet | CVE-2018-13382 | Authentication Bypass |
| MikroTik | CVE-2018-14847 | Authentication Bypass |
| Netgear | CVE-2017-6862 | Remote Code Execution |
| Pulse | CVE-2019-11510 | Authentication Bypass |
| CVE-2021-22893 | Remote Code Execution | |
| QNAP | CVE-2019-7192 | Privilege Elevation |
| CVE-2019-7193 | Remote Inject | |
| CVE-2019-7194 | XML Routing Detour Attack | |
| CVE-2019-7195 | XML Routing Detour Attack | |
| Zyxel | CVE-2020-29583 | Authentication Bypass |
By exploiting these vulnerabilities, the Chinese-sponsored threat actors have established broad infrastructure networks that helped them further compromise an even wider range of public and private sector targets.
The NSA, CISA, and the FBI also urge US and allied governments, critical infrastructure, and private industry organizations to apply a list of mitigation measures that would help decrease the risk of similar attacks breaching their networks.
The federal agencies advise organizations to apply security patches as soon as possible, disable unnecessary ports and protocols to shrink their attack surface, and replace end-of-life network infrastructure that no longer receives security patches.
They also recommend segmenting networks to block lateral movement attempts and enabling robust logging on internet-exposed services to detect attack attempts as soon as possible.
This joint advisory comes after two others that shared info on tactics, techniques, and procedures (TTPs) used by Chinese state-sponsored hackers (in 2021) and publicly known vulnerabilities exploited in their attacks (in 2020).
[ad_2]
Source link